Njsscan – A Semantic Aware SAST Tool That Can Find Insecure Code Patterns In Your Node.js Applications
njsscan is a static application testing (SAST) tool that can find insecure code patterns in your node.js applications using simple pattern matcher from libsast and syntax-aware semantic code pattern search tool semgrep.
Installation
pip install njsscan
Requires Python 3.6+ and supports only Mac and Linux
Command Line Options
$ njsscan
usage: njsscan [-h] [--json] [--sarif] [--sonarqube] [--html] [-o OUTPUT] [-c CONFIG] [--missing-controls] [-w] [-v] [path ...]
positional arguments:
path Path can be file(s) or directories with source code
optional arguments:
-h, --help show this help message and exit
--json set output format as JSON
--sarif set output format as SARIF 2.1.0
--sonarqube set output format compatible with SonarQube
--html set output format as HTML
-o OUTPUT, --output OUTPUT
output filename to save the result
-c CONFIG, --config CONFIG
Location to .njsscan config file
--missing-controls enable missing security controls check
-w, --exit-warning non zero exit code on warning
-v, --version show njsscan ve rsionExample Usage
$ njsscan test.js
- Pattern Match ████████████████████████ ;████████████████████████████████████ 1
- Semantic Grep ███████████████████████████ 160
njsscan: v0.1.9 | Ajin Abraham | opensecurity.in
╒═════════════╤═══════════════════════════════════════════════════	 552;═══════════════════════════════════════════╕
│ RULE ID │ express_xss │
├─────────────┼─────────────────────────────────────────────────────────────── ────────────────────────────────┤
│ OWASP │ A1: Injection │
├─────────────┼──────────────────────────────────────────────────────────────────────────^ 72;────────────────────┤
│ CWE │ CWE-79: Improper Neutralization of Input During Web Page Generation ('Cross-site Scripting') │
├─────────────┼──────────────────────────────────────────────────────────────────────────────────────& #9472;────────┤
│ DESCRIPTION │ Untrusted User Input in Response will result in Reflected Cross Site Scripting Vulnerability. │
├─────────────┼───────────────────────────────────────────────────────────────────────────────────────────────┤
│ SEVERITY │ ERROR │
├─────────────┼───────────────────────────────────────────────────────────────────────────────────────────────┤
│ FILES │ ╒═══════_ 52;════════╤═══════════════════════════════════════════════╕ │
│ │ │ File │ test.js │ │
│ │ ├────────────────┼───────────────────────────────────^ 72;───────────┤ │
│ │ │ Match Position │ 5 - 46 │ │
│ │ ├────────────────┼───────────────────────────────────────────────┤ │
│ │ │ Line Number(s) │ 7: 8 │ │
│ │ ├& #9472;───────────────┼───────────────────────────────────────────────┤ │
│ │ │ Match String │ const { name } = req.query; │ │
│ │ │ │ res.send('<h1> Hello :' + name + "</h1>") │ │
│ │ ╘════════════════╧════λ 2;══════════════════════════════════════════╛ │
╘═════════════╧══════════════════════════════════════════════════════════════════════════════	 552;════════════════╛nodejsscan SAST
nodejsscan, built on top of njsscan provides a full fledged vulnerability management user interface along with other nifty integrations.
See nodejsscan
Python API
>>> from njsscan.njsscan import NJSScan
>>> node_source = '/node_source/true_positives/sqli_node.js'
>>> scanner = NJSScan([node_source], json=True, check_controls=False)
>>> scanner.scan()
{
'templates': {},
'nodejs': {
'node_sqli_injection': {
'files': [{
'file_path': '/node_source/true_positives/sqli_node.js',
'match_position': (1, 24),
'match_lines': (4, 11),
'match_string': 'var employeeId = req.foo;\n\nvar sql = "SELECT * FROM trn_employee WHERE employee_id = " + employeeId;\n\n\n\nconnection.query(sql, function (error, results, fields) {\n\n if (error) {\n\n throw error;\n\n }\n\n console.log(results);'
}],
'metadata': {
'owasp': 'A1: Injection',
'cwe': "CWE-89: Improper Neutralization of Special Element s used in an SQL Command ('SQL Injection')",
'description': 'Untrusted input concatinated with raw SQL query can result in SQL Injection.',
'severity': 'ERROR'
}
}
},
'errors': []
}Configure njsscan
A .njsscan file in the root of the source code directory allows you to configure njsscan. You can also use a custom .njsscan file using --config argument.
---
- nodejs-extensions:
- .js
template-extensions:
- .new
- .hbs
- ''
ignore-filenames:
- skip.js
ignore-paths:
- __MACOSX
- skip_dir
- node_modules
ignore-extensions:
- .jsx
ignore-rules:
- regex_injection_dos
- pug_jade_template
severity-filter:
- WARNING
- ERRORSuppress Findings
You can suppress findings from javascript source files by adding the comment // njsscan-ignore: rule_id1, rule_id2 to the line that trigger the findings.
Example:
app.get('/some/redirect', function (req, res) {
var target = req.param("target");
res.redirect(target); // njsscan-ignore: express_open_redirect
});CI/CD Integrations
You can enable njsscan in your CI/CD or DevSecOps pipelines.
Github Action
Add the following to the file .github/workflows/njsscan.yml.
name: njsscan
on:
push:
branches: [ master, main ]
pull_request:
branches: [ master, main ]
jobs:
njsscan:
runs-on: ubuntu-latest
name: njsscan check
steps:
- name: Checkout the code
uses: actions/checkout@v2
- name: nodejsscan scan
id: njsscan
uses: ajinabraham/njsscan-action@master
with:
args: '.'Example: dvna with njsscan github action
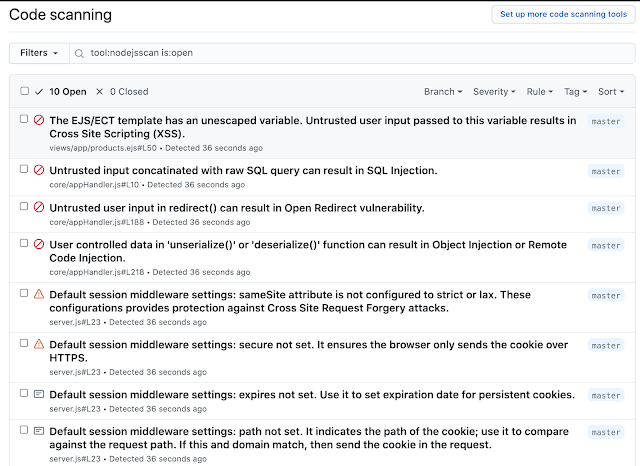
Github Code Scanning Integration
Add the following to the file .github/workflows/njsscan_sarif.yml.
name: njsscan sarif
on:
push:
branches: [ master, main ]
pull_request:
branches: [ master, main ]
jobs:
njsscan:
runs-on: ubuntu-latest
name: njsscan code scanning
steps:
- name: Checkout the code
uses: actions/checkout@v2
- name: nodejsscan scan
id: njsscan
uses: ajinabraham/njsscan-action@master
with:
args: '. --sarif --output results.sarif || true'
- name: Upload njsscan report
uses: github/codeql-action/upload-sarif@v1
with:
sarif_file: results.sarifGitlab CI/CD
Add the following to the file .gitlab-ci.yml.
stages:
- test
njsscan:
image: python
before_script:
- pip3 install --upgrade njsscan
script:
- njsscan .Example: dvna with njsscan gitlab
Travis CI
Add the following to the file .travis.yml.
language: python
install:
- pip3 install --upgrade njsscan
script:
- njsscan .Circle CI
Add the following to the file .circleci/config.yaml
version: 2.1
jobs:
njsscan:
docker:
- image: cimg/python:3.9.6
steps:
- checkout
- run:
name: Install njsscan
command: pip install --upgrade njsscan
- run:
name: njsscan check
command: njsscan .Docker
Prebuilt image from DockerHub
docker pull opensecurity/njsscan
docker run -v /path-to-source-dir:/src opensecurity/njsscan /srcBuild Locally
docker build -t njsscan .
docker run -v /path-to-source-dir:/src njsscan /src